July 29, 2021

- Oman reports a 25% increase in cybercrimes in 2020.
- Consumers and businesses in Oman suffered more than 190,000 phishing attacks* at the peak of the Covid-19 pandemic.
- After declining in 2019, phishing increased in 2020 to account for 1 in every 4,200 emails**.
Have you ever received an email from a big organization or a trusted source usually offering an unbelievable scheme or a hefty amount of money? The chances are quite high. Such emails are targeted to trick users to give out their personal information or sometimes even direct them to play out a malicious attachment. You may or may not have clicked it. However, the sad reality is that millions of such emails are sent out on a daily basis by hackers or cybercriminals and unfortunately a lot of innocent people fall for it. In most cases, the senders remain unaware.
In the recent past, there has been a massive upsurge in cyber-attacks on companies, government and individuals globally. Within just one quarter, more than 2.5 million phishing attacks were identified across the Middle East. Apparently, cases of fraud and extortions have become most prominent types of crime. Unlike older times, the sophistication of threats has upgraded with the evolving technologies such as artificial intelligence, machine learning, internet of things (IoT), and 5G.
On top of this, the pandemic has forced organizations to work from home. Since the outbreak of Covid-19, remote working has become the need of the hour. In 2020, companies across the world made a shift almost overnight to working from home. With that, they also let their guards down and became more prone to new cybersecurity threats that may have impacts for many years to come. In a recent survey, numerous organizations have accepted increased cybersecurity concerns due to their new remote working practices.

The fact is that such cyber threats are not going away. With newer threats emerging every day, they seem to continue to develop and broaden. The big question is how to protect your business or yourself from them?
HERE’S THE ANSWER:
DMARC – Domain-based Message Authentication, Reporting and Conformance
In simple words, DMARC is a standard email validation system designed to detect when someone else uses your domain without authorization. DMARC policy is conceptualized to prevent email spoofing, a form of disguising emails from an unknown source as being from a known, trusted source. The validation system for Email allows spoofing to be detected and prevented. It is used by organizations to block the delivery of unauthenticated emails. With the power of DMARC, organizations can have visibility into both legitimate and fraudulent emails sent using a company’s domain names.
First-ever published in 2012, the DMARC standard was aimed at preventing email abuse and providing email security protocol. Eventually, several industry leaders worked together to create the DMARC specification. PayPal, Google, Microsoft and Yahoo released DMARC to the world to authenticate emails. It was quickly adopted by security experts in the field of the financial industry. Since then, the policy of DMARC is being adopted across companies, across industries. At the moment, DMARC policy is extensively recognized by email marketers for ensuring foolproof online security.
What are DMARC Policies?
There are three DMARC policies available for mitigation.
1.Monitor Policy: (none)
It is known as a monitoring policy because it helps you gain an insight into your Email channel. The ‘none’ policy instructs that Email receivers send DMARC reports to the address published in the RUA or RUF tag of the DMARC record. This policy only provides insight into the email channel and tells who’s sending email on behalf of a domain. But it will not instruct email receivers to handle emails differently if they fail the DMARC checks. This policy will not affect the deliverability.
2.Quarantine Policy: (quarantine)
The quarantine policy of DMARC directs email receivers to put emails in the spam folder on failing the DMARC checks. Alternatively, if emails pass the DMARC checks they get placed in the primary inbox of the receiver. According to the quarantine policy, the impact of spoofing will be mitigated, but spoof emails will still be delivered to the receiver (in the spam folder).
3.Reject Policy: (reject)
The reject policy of DMARC ensures that no email gets delivered on failing the DMARC checks. And emails that pass the DMARC checks, make their way straight to the primary inbox of the receiver.
Furthermore, these settings can be customized as per the requirement. For instance, the server can be instructed to send only 10% of emails with a failed check to the spam folder using the ‘quarantine’ policy and the rest of the 90% doubtful emails can be scanned under the ‘none’ policy. DMARC gives you much more control than in the case of DKIM and SPF authentications as it empowers you to have a complete overview of the emails that are being sent.
With these settings of DMARC, the security teams of an organization can identify and halt any unapproved emails being sent from their domains. Thereby, it helps them protect their customers, employees, partners and associate from potential exploitation by cyber criminals. Through this type of central power, companies are able to intimate the receivers to reject the mail if their security checks are not aligned.

WHY IS DMARC IMPORTANT
Today, the world relies on technology more than ever. With over 66% of the world’s population using the internet, there are more than 5 billion email accounts, and you know that no other channel has a wider reach than Email. This is why, emails have been a preferred channel for malicious purposes used by cybercriminals. It is said that all businesses with a website and Email are vulnerable to cyber-attack.
A cyberattack in any form can lead to serious, devastating consequences for any organization. In the worst-case scenario, it can even cost a company its reputation through the loss of consumers’ and partners’ trust. Not to mention the irreversible loss of critical data, such as source files or intellectual property. Many high-status data breaches that made media headlines in the past have suffered huge losses.
Although, over the period of time, several companies have adopted measures to elevate their cybersecurity. But a recent survey clearly shows that 95% of all hacking attacks and data breaches involve ‘email’. Therefore, it is of utmost importance that organizations adopt and implement a strong cybersecurity approach.
This is where DMARC policy plays a vital role. Not only does it provide a complete insight into email channels but it also makes phishing attacks visible to the owner. DMARC also helps in mitigating the impact of malware attacks, prevents spoofing, protects against brand abuse, scams, and avoids business Email compromise.
On one hand, it helps protect customers and the brand, and on the other, it discourages cybercriminals who are less likely to go after a brand with a DMARC record. It is like bulletproof security where cybercriminals know their chances of spoofing are close to none with DMARC records. So they don’t even attempt it. Instead, they try and hunt for easier targets with no security.
A simple fact of cybersecurity is that prevention is always better and more cost-effective than recovery. And DMARC does provide surefire protection to online businesses and individuals. Besides, it does not need to be integrated into an existing set of operations. Instead, it can be very well included in the system at an early stage.

HOW DOES DMARC WORK
In simple words, DMARC allows senders to specify that their Emails are safe or protected. It also tells the recipient what to do in case of authentication failure (for example reject the message or send it to the junk/spam folder).
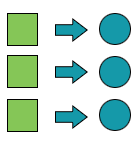
Technically, it’s not completely a new thing. The DMARC application makes use of the existing authentication techniques like Sender Policy Framework (SPF) and Domain Keys Identified Mail (DKIM) and performs an advanced check on each email. Then it instructs an inbound mail server to either verify the trusted emails or quarantine or reject the spoofed ones.
Through the DNS records, the DNS owner can specify its own authentication procedure (known as a DMARC policy) and look into the details as in who is sending emails on behalf of their domain. This information helps identify if any fraudulent email is being sent and allows email senders and receivers to determine the authenticity of an email.
DMARC allows managing email infrastructure in a meticulous and controlled manner. Its reporting capabilities help increase Email deliverability. Or else it would be risky to change email channels since genuine emails might fail and illegitimate ones might pass due to such changes.
Implementing DMARC helps block malware, phishing attacks, and minimize the number of potentially malicious emails and attachments that can make their way into your inbox. According to the Global Cyber Alliance, more than 4.8 billion inboxes are currently protected by DMARC policies across the world.
DMARC also makes it possible to train the email receivers about how to handle emails that do not pass the DMARC checks. It can be done by defining a policy that can instruct an ISP. As per the settings, the email receivers check for valid SPF and DKIM records for any incoming messages. Post these checks, a message can be considered as DMARC compliant or DMARC failed. Then the email receiver verifies the authentication status of the message. Based on the set DMARC policy, the message is treated in a different way.
The service, provided by the National Digital Certification Center (NDCC) at the Information Technology Authority (ITA), allows all Omani Citizen and residents to use the government’s electronic services and transactions at a higher level of security, authenticity, integrity, and confidentiality.
Furthermore, the service is also protected by the Oman eTransaction law. This provides all users with the level of trust, given that all eTransactions carried out using an Oman PKI will be held to the same legality standards as handwritten signatures and the physical presence of the user.
With Oman PKI in place several government services can now be carried out online through digital validation of documents, without even requiring the physical presence of the user. This will not only save time, money, and effort, but will also make several government services accessible from everywhere and anytime.
At present there are primarily two ways to get your own digital identity registered in the country – via your identity card or via your mobile SIM card. The former is available for free and only requires the ID or resident card to be activated with your personal digital identity.
Signing using your ID or resident card would require the use of a card reader and, as such, is used primarily for signing documents on desktops. In order to do so, once the reader is plugged into said desktop, you would only need to review the document, add in your personal 4-digit code to sign, save, and then send it.
For mobile signing, you would be required to first obtain or replace your existing SIM with one that supports PKI. Once activated, the process is the same– review the document on your mobile, add in your personal 4-digit code to sign, save, and send. It really is that simple.

BENEFITS OF IMPLEMENTING DMARC
- Ensure Security – Put an end to the unauthorized use of your email domain. Protect your business from spam, fraud, and phishing. Save your customers, employees and reputation from cybercrime.
- Drive Visibility – Gain visibility into who and what across the internet is using your email domain to send emails.
- Gain Control – Take out-and-out control over emails sent from your domains. If anyone misuses your domain, you will instantly have it displayed in the DMARC report.
- Safe Identity – Make your email easy and harmless to identify across the huge and growing footprint of DMARC-capable receivers. Improve trust in the emails sent by your organization.
- Avoid Threats – Dive deeper into threats and assess cyber information. Safeguard your own technological assets.
- Legit Delivery – Follow the best practices that even mega companies of the world make use of to deliver their emails. Let your emails land in the primary inbox of the receiver without any risk.
The Crux of the Matter
With the growing digitization of everyday life, the power of emails should not be underestimated. There is a whole industry based on email marketing. Besides, all types of organizations rely on emails for their communication with customers, partners, and associates. With this logic, companies are also liable to keep their customers safe from exploitation by cybercriminals. And in the case of emails, it goes without saying that it is even more important to keep their own brands safe too. The bigger your company, the greater the risk. DMARC is a highly effective tool to fight all possible malicious activities in the world of email. Its execution helps businesses and organizations maintain trust and saves them from losing money, data and efforts.
Some studies prove when emails are received from DMARC-secured domains, they are much more likely to be perceived as legit than those that came without any security. Also, an email with a DMARC check will be way more likely to be delivered.
It’s absolutely worth repeating one last time – the most effective way of protecting yourself from unauthorized emails or malicious practices online is DMARC. Period.
Take control today. Protect your business with our DMARC solutions. To know more reach out to us via phone on +968 2417 1111 or email us.
*findings by Kaspersky
**(Symantec)