- Network Security
- Fully Managed
- ISO27001 for Information Security Management System
- 24X7X365 SOC Security Operations Center
Network Zero Day Attack Prevention Prevent Advanced Threats with our Zero Day Attack Prevention Services and Save Your Business from a Week of Data Loss.
Prevent and Beat Malware Hands Down

Prevention is the best strategy for protecting your business from a malware attack. Manual malware removal is a complicated process even for savvy users.
Oman Data Park offers Zero Day Attack Prevention as a managed service. This service will scan for attacks, detect any threats present, and alert your business to take swift action.
Constant vigilance is achieved through our Security Operations Center. They use specific tools to scan for viruses at the network level based on heuristics, known threats, and virus signatures.
The service is endpoint agnostic, meaning it can be deployed regardless of the devices end users are using.
Pricing plans are made available following an initial consultation.
Key Benefits
- Advanced Protection for your business through blocking of customized and unknown malware that evades real-time protection by other systems.
- Use of Artificial Intelligence (AI) to protect your business against unknown attacks by detecting attack profiles from known threats and applying them to evaluate new problems.
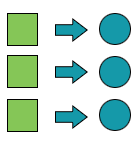
- Multi-stage data analysis process with machine learning, behavioral analysis, and other techniques to characterize and confirm previously undiscovered malicious content.
- Continuity for your business-critical software without the risk of cyberattacks.
Features
- Deep packet inspection engine.
- Deep content inspection.
- Intrusion prevention.
- Signature-based AV scanning, Network layer.
- Heuristic-based AV scanning, Network layer.
- Static-based AI AM scanning, Network layer.
- Behavioral based AI AM Analysis.
- Real time Zero day prevention mode.
- Endpoint agnostic for BYO or IOT devices.
Businesses Are Constantly Vulnerable and Require Investment into Cybersecurity

According to statistics, the rise of ransomware and botnets has made it easier for cybercriminals to infect businesses with viruses and other malicious software. Ransomware attacks worldwide rose 350% in 2018.
Ransomware attacks are estimated to cost $6 trillion annually and 75% of companies infected with ransomware were running up-to-date endpoint protection.
Malware is a major problem worldwide. While Proactive measures such as antivirus software can help prevent malware infections, they aren’t sufficient to deal with the more advanced threats that evade detection.
The most advanced threats are known as zero day attacks. They are called this because the malicious software is unknown prior to the attack.
Protecting against a zero day attack is very difficult. Like many forms of cyber defense, the best protection has several components.
How Much Data Does Your Business Process in One Week?
 According to reports 43% of cyber attacks target small business owners who are often unaware of their risk until it’s too late. 34% of businesses hit with malware took a week or more to regain access to their data.
According to reports 43% of cyber attacks target small business owners who are often unaware of their risk until it’s too late. 34% of businesses hit with malware took a week or more to regain access to their data.
Advanced threats have become so evasive that current technologies have proven to be unreliable for malware. Enterprise security strategies are shifting from prevention to post-breach detection and remediation. While detection and remediation will always be an important part of best practices, effective threat prevention is still the first order of business.
The problem with detecting and removing malware is that it is not always easy or even possible. As a result, many organizations struggle to detect and remove the malware in time before the damage is done.